Swiss Identity Verification
Executive Overview & Technical Whitepaper
Swiss Identity Verification is developed to meet Switzerland’s standards of privacy, consent, and minimal user-data exposure. All collected biometric and identity information is protected using Swiss-grade encryption and user-controlled data lifecycle principles.
The Future of Fast, Deepfake-Resistant ID Verification
Swiss Identity Verification is our next-generation identity verification platform, powered by our proprietary technology, Continuous Scene Verification CSV. CSV verifies the user’s face and ID document while analyzing the environment (the physical consistency of the scene) — all within a single continuous 2-second video. This novel, scene-level analysis of face, ID, and environment delivers a faster and smoother onboarding experience with industry-leading deepfake resistance.
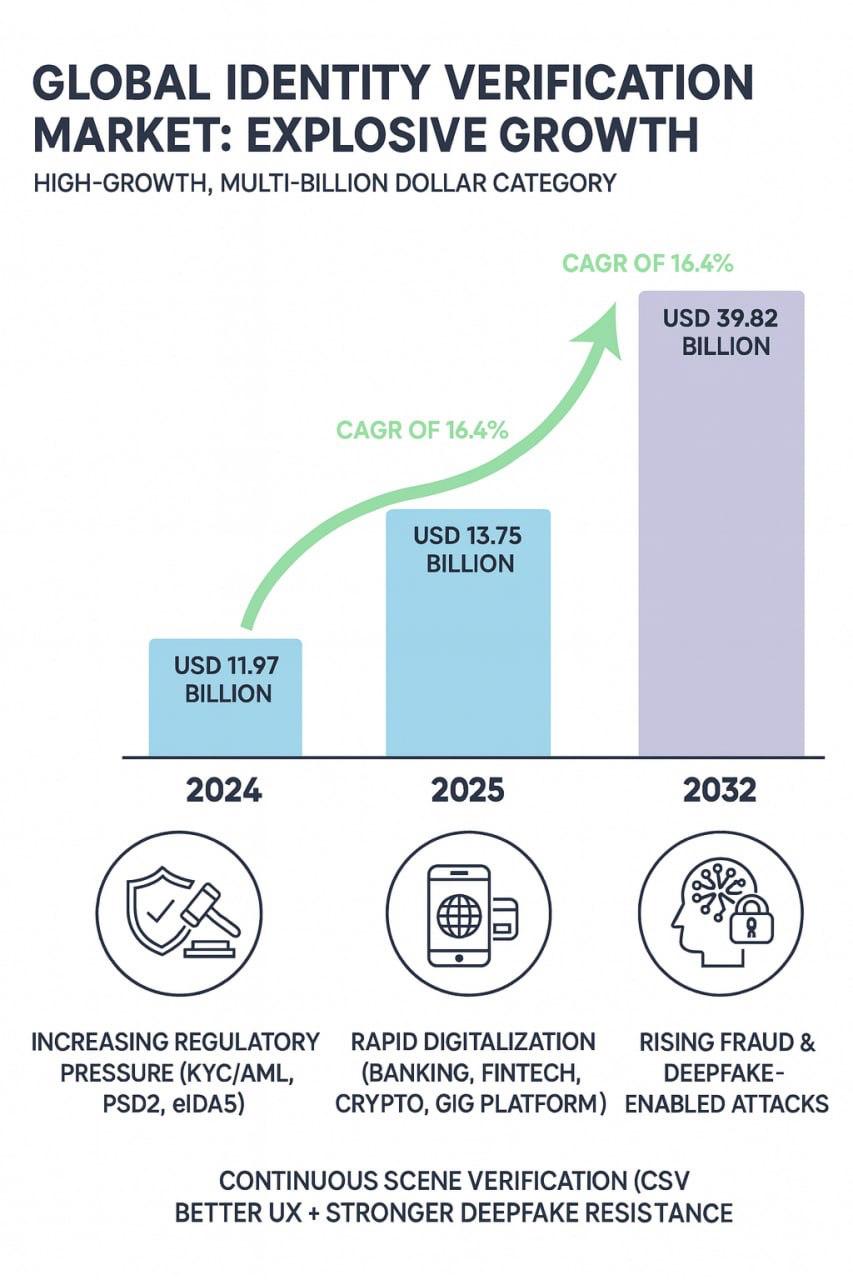
Today, customers abandon onboarding and KYC flows because they are forced to capture perfect document photos and perform awkward liveness actions like blinking, smiling, or turning their heads. At the same time, deepfake-driven fraud is accelerating faster than traditional identity verification systems can evolve.
To reduce friction, many providers have shifted from active liveness (blink, turn, smile) to passive or semi-active liveness, where the system attempts to detect real presence without explicit user actions. While this improves user experience, it still requires separate document photos, introduces delays, and remains vulnerable to evolving deepfake attacks.
Our technology – Continuous Scene Verification (CSV) – solves these problems by verifying the user’s face and ID while checking that lighting, shadows, and motion behave consistently across the face, hands, and ID, confirming they exist in the same real physical scene – all within a short 2-second video clip where the user simply brings their ID next to their face. No photo uploads, no switching steps, no instructions, and no gestures such as blinking or head-turning. CSV represents the evolution beyond passive liveness, collapsing liveness, document capture, and scene analysis into one seamless step and delivering industry-leading resistance to deepfake attacks: today, no AI can simultaneously forge a live face, real ID motion and hologram physics, hand and its motion, face–hand–ID motion geometry consistency, physical occlusion behavior (when the ID partially covers the face) and lighting/shadow consistency across face, ID, hands, and surrounding scene in real time.
This creates:
• Faster identity verification experience
• Higher deepfake resilience (i.e. materially reduced fraud)
• Higher conversion rates for our clients
CSV is the next-generation identity verification layer that replaces the document photo, selfie, and liveness steps inside any KYC or onboarding flow — modernizing decade-old legacy processes with a frictionless, deepfake-resilient standard.